Ruishu information experts interpret ChatGPT: AI is the future of network security

[ad_1]
Since Chatting became popular all over the world, people are surprised to find that this AI chat robot can not only easily talk to humans, but can even write code.
On forums, programmers post jaw-dropping examples of code generation. From connecting cloud services to porting Python code to Rust, ChatGPT has demonstrated extraordinary capabilities in some basic programming tasks. This makes people worry that ChatGPT will become a helper for hackers.
So how will the arrival of ChatGPT affect the field of network security? Will ChatGPT be directly used by hackers? In which network security fields can it be applied? Will it become the development direction of future network security technology?
In the face of many questions brought by ChatGPT, Ruishu information experts shared their views.
ChatGPT network security application status
ChatGPT is a natural language processing tool driven by AI technology, which can chat and communicate like humans. For the topic of “whether it will constitute a network security threat”, ChatGPT obviously also has its own views:
“No, ChatGPT does not pose a cybersecurity threat. It is a language model developed by OpenAI designed to generate text based on the input it receives. However, it is important to remember that any technology can be misused and users have Responsibility to protect their systems and data. Also, exercise caution when sharing sensitive information as it may be accessible to third parties.”
At the same time, ChatGPT also added: “If it falls into the wrong hands, it may be used maliciously”, “ChatGPT may be used to grab sensitive information from the Internet, such as personal data or financial information.”
In other words, whether ChatGPT is a threat or not depends on the purpose of the user.
In this regard, Ruishu information experts said that, like any technology, once ChatGPT is used by people with ulterior motives, it will also become a tool for doing bad things. For example, use ChatGPT to generate phishing emails or malicious code, or use ChatGPT to find loopholes in code.
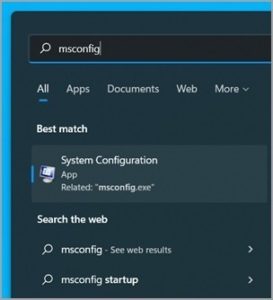
Figure: Auto-reply after asking ChatGPT how to generate phishing emails
“For junior hackers, ChatGPT can indeed improve the attack level, especially ChatGPT has greatly improved the efficiency of obtaining information and applying it, and lowered the attack threshold; but for advanced hackers, to improve the attack level, more needs their own special research And accumulation, ChatGPT can only play an auxiliary role”, said Ruishu information expert.
Of course, ChatGPT, as a technical “double-edged sword”, can also be applied to the field of network security protection. In this regard, ChatGPT also provides 15 possible application directions:
Automated threat intelligence analysis: use ChatGPT for natural language processing and sentiment analysis, and automate the analysis and identification of threat intelligence.
Malicious code detection: Use ChatGPT for text analysis and classification, and automatically detect and analyze malicious code.
Network security incident response: use ChatGPT to perform natural language processing and semantic analysis on network security incidents, and quickly respond to and resolve network security incidents.
Intrusion detection based on machine learning: Use ChatGPT to train and predict machine learning models to achieve intrusion detection based on machine learning.
Intelligence collection and analysis: Use ChatGPT to automate the collection and analysis of network intelligence to provide support for network security decisions.
Automated Vulnerability Detection: Use ChatGPT for natural language processing and semantic analysis to automatically discover and detect vulnerabilities in systems and applications.
Intelligent security consultation: use ChatGPT for natural language processing and intelligent question answering to provide users with real-time security consultation and advice.
Identity verification and authorization management: Use ChatGPT to automatically verify and authorize the user’s identity to protect the security of the system and data.
Intelligent risk assessment: use ChatGPT for natural language processing and data analysis to provide enterprises and organizations with intelligent risk assessment and management services.
Automated Security Testing: Use ChatGPT for natural language processing and semantic analysis to automate testing and evaluate the security performance of systems and applications.
Automated security audit: Use ChatGPT for natural language processing and data analysis to automate system and application security audits and assessments.
Prediction and early warning of security incidents: Use ChatGPT for natural language processing and machine learning to predict and early warning network security incidents.
Artificial intelligence firewall: use ChatGPT for natural language processing and machine learning, develop an intelligent firewall system, and realize automated threat defense and security protection.
Intelligent data classification and protection: Use ChatGPT for natural language processing and text analysis to automatically classify and protect sensitive data.
Intelligent encryption and decryption: Use ChatGPT for natural language processing and encryption algorithms to realize intelligent encryption and decryption services and protect data confidentiality and integrity
Ruishu Information experts said that the above scenarios are technically possible, but the codes or suggestions generated directly through the ChatGPT dialogue cannot be directly applied in the production environment without any modification and testing. If you want to use it in a real production environment, you still need to do more precise training in the security field in order to apply this new AI technology more effectively.
Security offensive and defensive posture using AI technology
The explosion of ChatGPT has pushed AI technology from behind the scenes to the front stage, but in fact, the research on AI in the field of network security has already started.
At the 2017 Black Hat Conference in the United States, hundreds of network security experts voted to predict whether hackers will use AI technology to engage in criminal activities in the next few years, and 62% of them said yes.
Due to the ability of AI automation and intelligence, hackers can accelerate the speed of attack, attack as many target users as possible in the same time, and reduce their own risks. Therefore, in recent years, the incidents of using AI technology to carry out network attacks have increased rapidly.
“Hackers have already used AI technology and cloud services to build a black industrial chain,” said Ruishu information experts. “For example, hackers will use AI technology to identify verification codes or simulate human operation behaviors to bypass the security protection of websites.”
For example, in the login verification of some websites, whether it is sliding a button or filling in a verification code, hackers can use AI to imitate the operation of a real person and successfully pass the verification.
“According to our observation, the accuracy of AI bypassing can even be as high as 100%. The higher the recognition rate, the higher the charges for illegal products, so hackers will spare no effort to improve the accuracy and efficiency of AI attacks,” Ruishu information expert express.
Although hackers have begun to use AI as a weapon, security vendors are also rapidly following the development of AI.
Taking Ruishu Information as an example, as early as 2017, it started research on AI technology in the field of security. As network attack means and methods are updated faster and faster, and attack features are becoming more and more hidden, Ruishu Information has added AI technology on the basis of its original “dynamic security” technology, subverting the traditional security protection based on features and rules The idea of leading security protection from static to dynamic, from passive to active.
Based on Ruishu Information’s “Dynamic Security + AI” technology, enterprises can build multiple security lines of defense:
The first line of defense, through dynamic security technology, flexibly uses various dynamic interference functions such as Web code obfuscation, JS obfuscation, front-end anti-debugging, cookie obfuscation, and man-in-the-middle detection to implement dynamic interference to attackers;
The second line of defense, by superimposing AI technology, conducts real-time analysis of highly concealed abnormal access behaviors such as simulated real people, to achieve more accurate human-machine identification, and to identify various known and unknown attacks.
Based on these two Ruishu innovative technologies, enterprises can realize integrated defense in multiple attack scenarios such as Bots automated attacks, 0day attacks, DDoS attacks, and API attacks.
In recent years, Ruishu Information has continued to improve in the research and development of AI technology, mainly including three directions:
Malicious content identification, including SQL injection, XSS and Webshell, etc.;
Attack behavior detection, including automatic threat identification, collaborative attack detection, and abnormal user behavior analysis;
Ransomware encryption detection, including ransomware encryption detection for file systems and databases.
At the beginning of 2022, in the “Third China Artificial Intelligence Competition” sponsored by the Ministry of Industry and Information Technology, the Cyberspace Administration of China and the Ministry of Public Security, Ruishu Information won the A-level certificate with the highest score in the competition of Webshell detection and recognition direction, which shows its strong strength AI strength.
AI may become the future of network security
Undoubtedly, AI has become a new-generation weapon in cyber offensive and defensive warfare, and no party has a choice but to use AI to arm itself. With the popularity of ChatGPT, will AI technology accelerate changes in the field of network security?
Ruishu Information experts believe that in the short term, AI and existing security technologies will coexist, but in the long run, AI is likely to subvert existing security technologies and reshuffle the competitive landscape of security vendors.
“At present, all security vendors are still in the stage of AI training and tuning models, and the market is still dominated by a large number of traditional security technologies. With the increase in computing power, the increase in data volume, and the reduction in costs, AI technology will have a quantitative change. In the process of qualitative change, at that time AI will replace traditional security technology and human work,” Ruishu experts said.
In his view, the emergence of ChatGPT has made the industry see the great potential of large models such as GPT, and its advantages cannot be underestimated:
First, with the addition of this type of AI technology, network security protection may become smarter and respond faster, and can protect against attacks that were previously unnoticed or unavoidable. At the same time, AIGC (generated AI) technology can also Automatically generate protection rules to greatly shorten attack response time.
Second, as an automated machine, AI can work around the clock without causing problems such as human fatigue, thereby reducing the pressure on security operators.
Third, based on excellent natural language processing, AI can run security product-related functions through dialogue instead of SQL statements, and automatically generate reports, thereby greatly reducing the threshold for using security products and making it easy for non-security professionals to use . In the future, security products may also integrate AI chatbots like ChatGPT to assist security managers in analyzing threat situations and giving possible disposal suggestions.
For this reason, Ruishu Information experts believe that the underlying GPT model of ChatGPT or other similar models will be widely used in the field of network security.
But it is worth noting that ChatGPT is not suitable as an AI basic model for direct application in the field of network security for fine-tuning. Ruishu experts pointed out that, on the one hand, because of the high training and operation costs caused by the ChatGPT super-large-scale model, not many enterprises can afford it even as an API open service; It is too likely to provide safe data to train the model based on ChatGPT.
Therefore, there should be an exclusive SecurityGPT for the network security industry, which can be used to train network security domain knowledge based on the GPT model, while reducing the size of the model while maintaining the performance of AI in the security field, and finding a balance between technology and cost.
It is understood that before ChatGPT became popular, Ruishu Information was already researching the GPT model, and the related technology is currently being developed in the laboratory. In the future, Ruishu Information plans to open the GPT interface to third-party calls, and build an ecosystem of AI applications in the security field with partners from all walks of life.
epilogue
The emergence of ChatGPT has made network security attacks easier and brought great risks to enterprises. Today, under the trend of escalating network security offensive and defensive confrontation modes, using AI to fight against AI will definitely be the future development direction. As an innovative manufacturer in the field of network security, Ruishu Information will continue to improve AI technology and build a new generation of active defense security system for the intelligent era for enterprise users.
[ad_2]
Source link